#
Category: Security
See all categories.
This tutorial explains some annotations used in Java Spring Security.
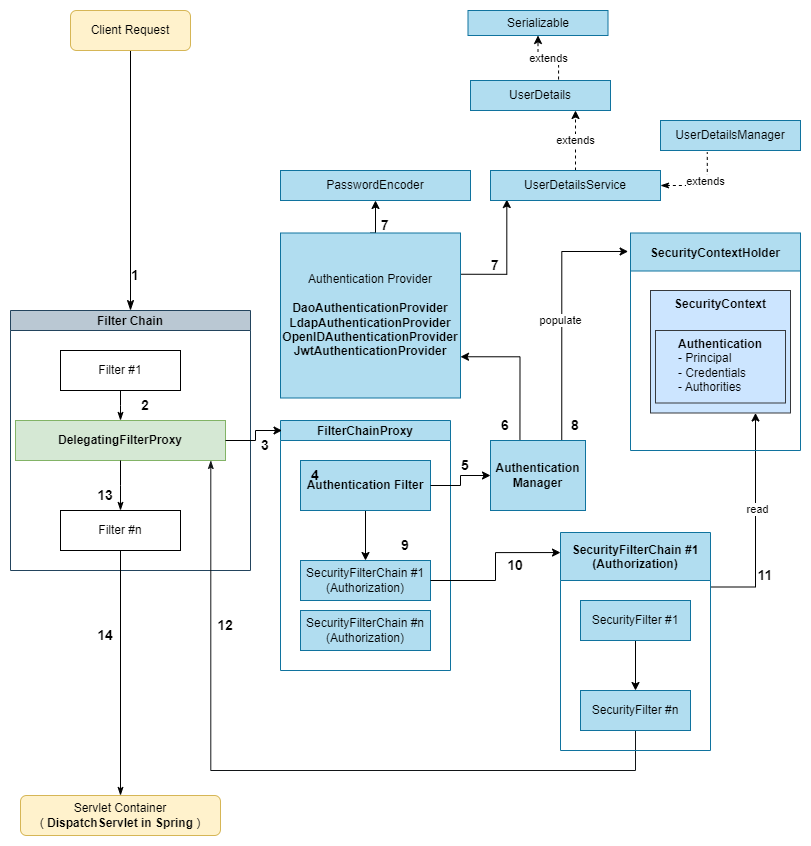
This tutorial is a Spring Security architecture overview.
This tutorial helps you to create a Spring Boot Service using Spring Security.

This tutorial helps you to call a PUT, POST, DELETE, PATCH request against a Spring Boot service secured using Spring Security.
This tutorial explains how we can disable the CSRF when using Spring Security.
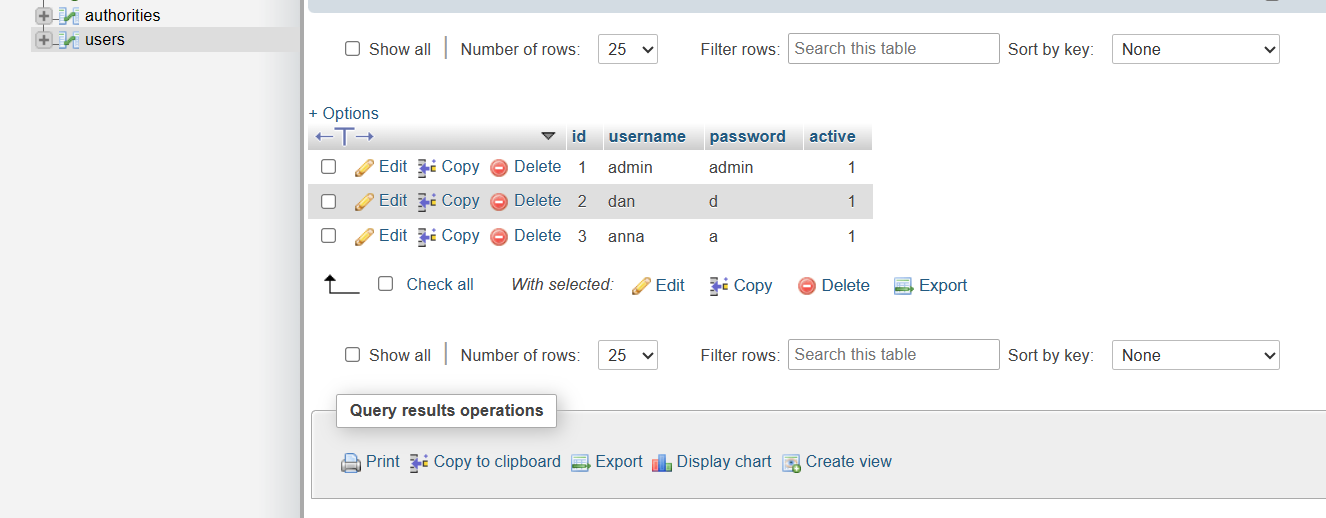
This tutorial explains to you how we can define users with passwords and keep this information into a MySql database.
This tutorial explains how we can authenticate into Spring Boot using Spring Security and credentials stored into a MySql database.
This tutorial explains how we can authenticate into Spring Boot using Spring Security and credentials and roles stored in memory.
This tutorial explains how we can authenticate into Spring Boot using Spring Security and credentials and roles stored in memory.
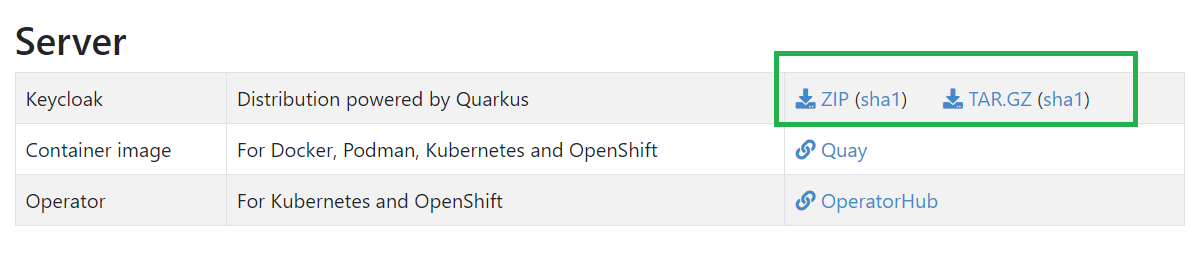
This tutorial explains how we can implement OAuth in Spring Boot using Spring Security 6 and Keycloak 20.
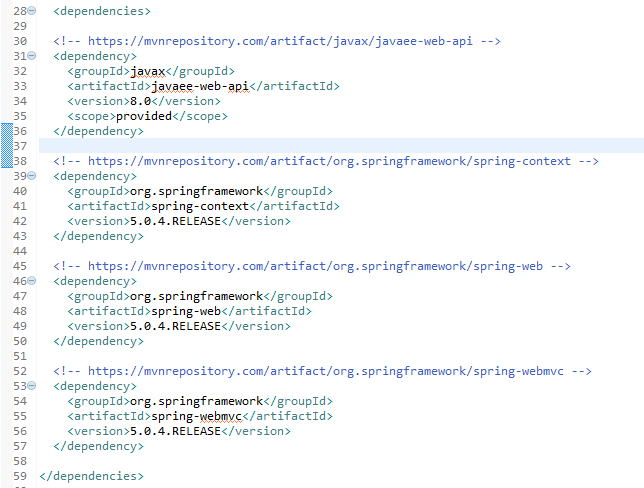
This tutorial explains to you how you can create a simple Spring simple mvc application with no security enforcement.

This tutorial explains to you how you can secure a Web Application with Spring 5.
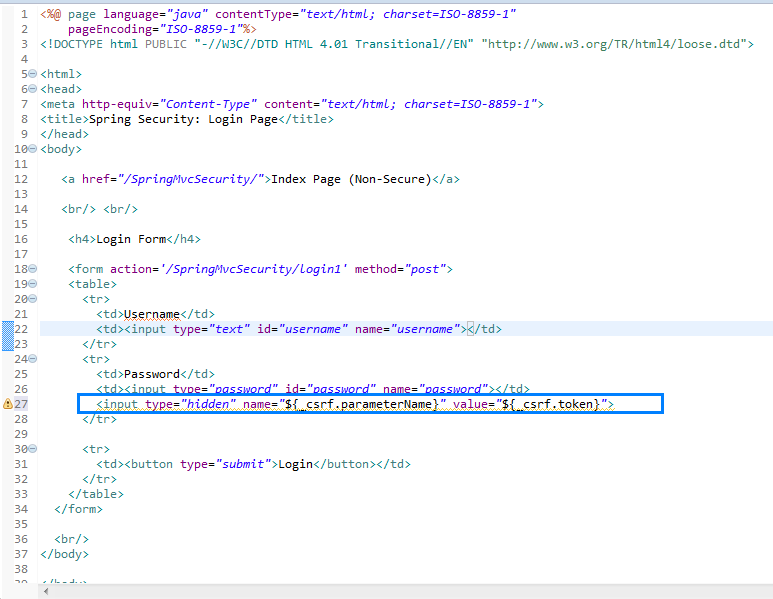
This tutorial explains to you how you can secure a Web Application with Spring 5 Security for Cross Site Request Forgery (CSRF).

This tutorial explains how you can create custom login form with Spring 5.
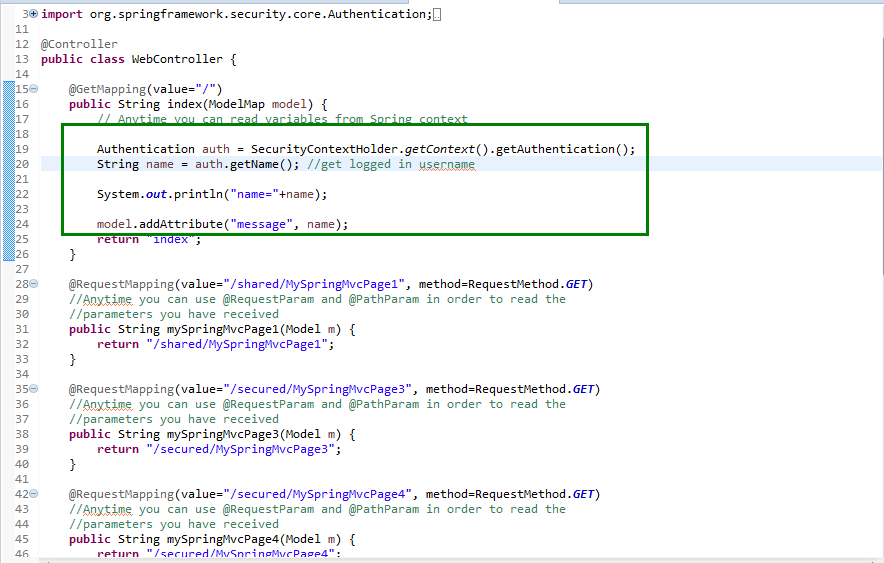
This tutorial explains how you can implement anonymous login in Spring 5.